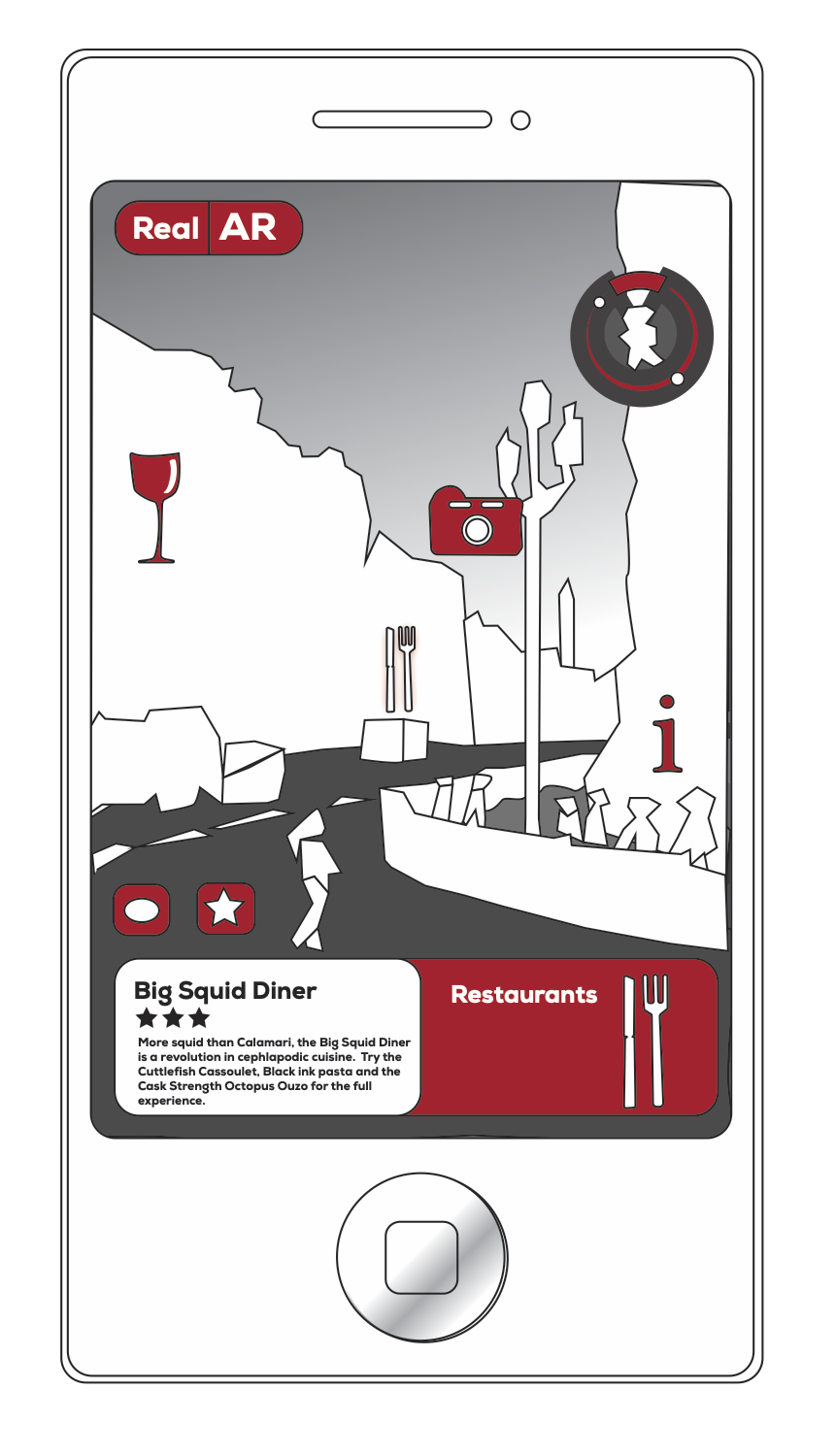
Augmented reality (AR) technologies supplement a live view of the real-world with interactive virtual objects. AR applications work by first sensing input, transforming sensed objects, and then displaying transformed objects to the user. A mobile AR browser can combine a live camera feed and GPS data from a smartphone to overlay virtual objects on the camera view in real-time. There are different AR channels that specify the content and how it is displayed, as well as what happens when certain objects come into view or are clicked by the user. AR channels include those that overlay historical pictures when viewing sightseeing landmarks, or display reviews for restaurants.
McPherson, Jana, and Shmatikov conducted an in-depth analysis of AR apps to assess their security and privacy risks. Using five classes of cyber attackers, they classified six types of vulnerabilities and provided corresponding engineering guidelines for securing AR functions. The researchers analysed the functional requirements of AR and tested for new vulnerabilities in their implementation. They then demonstrated new threats unique to AR browsers. The study looked at five classes of attackers: AR attackers, ad attackers, web attackers, curious AR services, and network attackers. They classified six new security and privacy vulnerabilities unique to AR browsers:
Access to device resources from outside the AR browser is possible currently because the AR browser can be accessed by any web content regardless of its origin. This means that attackers can gain access to a user’s camera and take pictures of the user and their surroundings. One solution the researchers recommend is that AR browsers apply more restrictions on channels, while giving more control to the user.
Automatic actions activated by images can be a problem in some AR browsers as the browser is constantly analyzing the camera feed. As soon as it recognizes an image associated with a channel, it automatically launches the channel’s content without a confirmation prompt. This could lead to fully-automated large scale tracking. For example, registering a channel associated with the image of a vehicle license plate could crowd source tracking of that vehicle. Any time a user scans their surroundings and that license plate comes up in the camera feed, the channel will be launched automatically and the plate’s location and surroundings are sent to the channel’s owner. AR browsers should inform the user about the origin of the AR content, the possibility of false matches and unexpected content.
AR service providers should prioritize removing functional and design flaws to improve the security of mobile AR browsers. The six categories of AR vulnerabilities and related guidelines for software engineers can help implement better security into existing AR browsers. User experience professionals should also integrate security and privacy warnings into mobile AR browsers so that the users are informed of the risks of their use.
Augmented reality apps present unique security and privacy risks which must be addressed.