Cybercriminals have recently turned to public Cloud providers such as Amazon Web Services, Microsoft Azure, and Google Cloud as platforms for launching Denial of Service attacks. They provide flexible, on-demand capacity and offer bandwidth which can be as much as 1,000 times higher than is possible with compromised home routers or IoT cameras. Internet Protocol (IP) spoofing, that is forging the source address of Internet data packets, is instrumental in many illegitimate online activities. For instance, criminals can initiate distributed denial of service (DDoS) attacks by sending request data packets to amplification servers, with the spoofed address of the victim as the return address. Cloud providers have thus recently implemented anti-spoofing filtering to prevent data packets with an incorrect address from entering and leaving their network.
Vlajic et al. examined the feasibility of attacks with public Cloud services from an offender’s perspective, based on real-world experimentation. The research is organized around three questions: 1) How is IP spoofing addressed in the acceptable-use and terms-of-service policies of Cloud service providers? 2) How effective are they in spotting and blocking outgoing spoofed IP packets generated by malicious customers? 3) How effective are they in spotting and blocking spoofed IP packets sent to their servers?
The authors examined the policies of 35 public Cloud service providers, including top players in the field (Amazon, Microsoft and Google) as well as a number of lesser-known companies. They experimented on 14 of those 35 providers, rejecting those which explicitly prohibited IP spoofing, or which required expensive or long-term subscriptions. The experiments evaluated the ability of providers not only to deal with spoofed IP packets, but also to spot and filter out invalid packets and addresses (for instance, private addresses and specific transmissions from Google‚‘s 8.8.8.8 server). The authors limited their tests to single packet probes, as they did not want to engage in any actual attack-like activity. Although larger volumes of spoofed data packets (as would be more realistic for a DDoS) might have produced different outcomes, the authors argue that there is no reasonable justification to allow any spoofed data packets from certain categories.
Out of the 35 surveyed Cloud providers, 19 (including Google Cloud and Microsoft Azure) make no direct reference to IP spoofing in their policies. Out of the 14 evaluated providers, only three originally allowed the transmission of spoofed IP packets. More concerning are the results of the second experiment, which show that most providers not only accept, but also automatically respond to spoofed IP packets. This implies that even if most Cloud providers successfully prevent potential hackers from using their services to launch spoofed-IP campaigns, they themselves are usually vulnerable to those campaigns, or could be used to reflect attacks on potential targets.
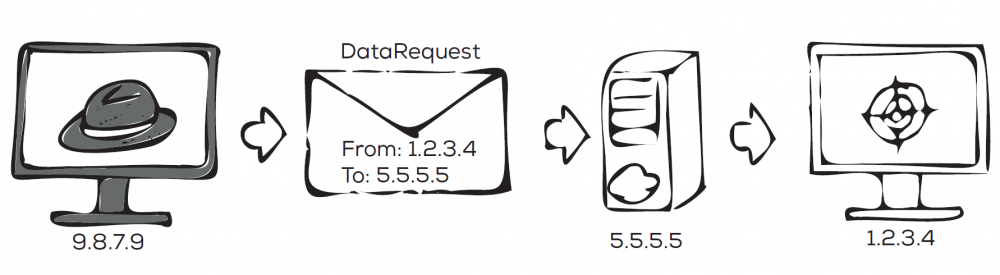
Most public Cloud providers block outgoing spoofed IP packets, but do not block incoming spoofed packets. This makes them potential attack targets.