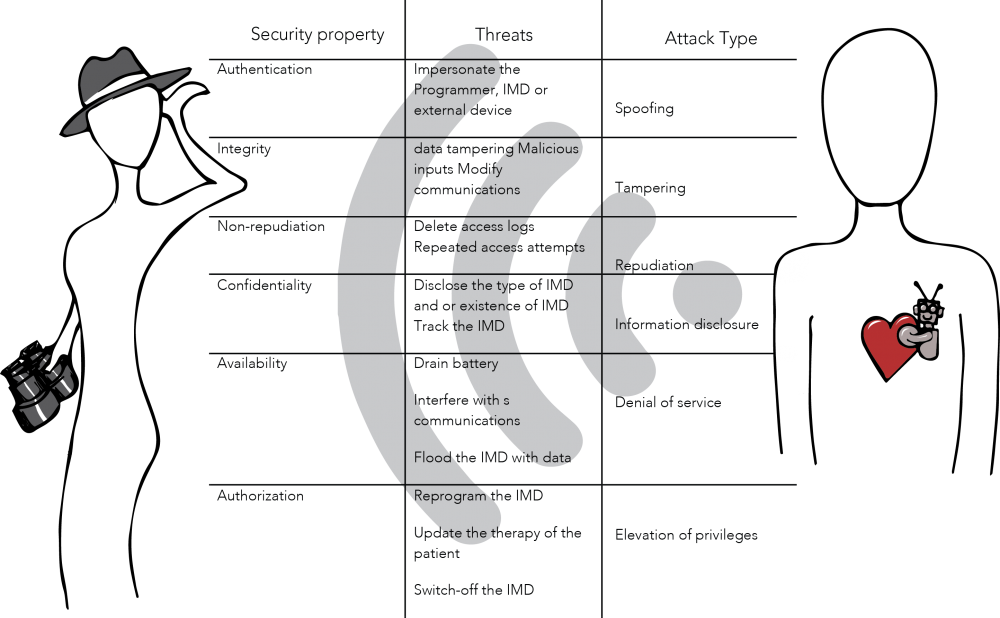
Implantable Medical Devices (IMDs) are electronic devices inserted into the body to treat, monitor or improve the function of a body part. IMDs can monitor part of the body and electrically stimulate organ function such as the brain and heart. Drug Delivery Systems (DDS) supply medication in a controlled, localized, and prolonged way. New IMDs have started to incorporate more advanced communications and computing capabilities to reduce cost and provide new diagnostic and treatment capabilities to healthcare providers. The wireless communication capabilities in IMDs and the development of Intra Body Networks (IBN) of medical devices present new security risks and challenges. Besides the magnification of existing threats to wireless networks such as eavesdropping and unauthorized data or operation access or modification, the mere existence of an IBN means the implant is no longer ‘‘invisible’’, as its presence could be remotely detected breaching the patient’s privacy.
Carmen Camara, Pedro Peris-Lopez, Juan E. Tapiador present a survey of security and privacy issues in IMDs, discuss the most relevant mechanisms proposed to address these challenges, and analyze their suitability, advantages, and main drawbacks. Providing security for IBNs present additional challenges, as an IMD must operate under two different modes: normal and emergency. Under normal operating conditions an IMD must ensure the security of its operation and preserve the privacy of the patient. Nevertheless, during an emergency the medical personnel must be able to access the implant rapidly and without restrictions.
IMDs have limitations on how security is implemented due to the severe restrictions on the use of energy, storage, and computing power. These limitations are strict as device failure or even communication latency due to security controls puts the patient’s safety at risk. Managing the tradeoff between safety and security is critical in the design of IMD security mechanisms. Security solutions are more complex because of the need to manage these practicalities.
Auditing, a basic security provision for recording events on a device, requires additional processing and storage either on the device or via an external device. It is also possible for an external device to control access to the IMD based certificates and lists, blocking or jamming unauthorized accesses. While the external device may overcome the resource limitations of the IMD they introduce complexity, make emergency access more difficult and are not totally effective. Communication channel and authentication processes could be abused to produce a Denial-of-Service attack or to deplete battery and memory resources; as a Resource Depletion (RD) attack. Solutions such as encryption are also resource expensive and do not prevent these attacks. The existing research on RD attacks in sensors networks are not directly applicable to IMDs since implants have more severe resource restrictions. Other security options such as proximity based controls, either using bounding protocols or switching though subcutaneous buttons or magnetic switches. Another option is the introduction of an IMD hub for managing extra-personal communications and security.
However, it is important to remember that these devices are implemented within a human body. Adding resources or hardware to improve security requires invasive surgery. Adding complexity and embedded software increases the risk of device failure and human injury.The trade off and tension between solutions means that the optimal choice is not certain. What is clear is that the design of security for IMDs requires careful consideration of the patient. The computer security industry has to be ready to provide robust solutions at the design phase and avoid the current develop-then-patch approach to security.
IMD security is hard and we don’t seem to be ready to implement meaningful security.